Find the best Secure Email Gateway Software
Compare Products
Showing 1 - 20 of 39 products
Sort by
Reviews: Sorts listings by the number of user reviews we have published, greatest to least.
Sponsored: Sorts listings by software vendors running active bidding campaigns, from the highest to lowest bid. Vendors who have paid for placement have a ‘Visit Website’ button, whereas unpaid vendors have a ‘Learn More’ button.
Avg Rating: Sorts listings by overall star rating based on user reviews, highest to lowest.
A to Z: Sorts listings by product name from A to Z.
MimeCast Email Security
MimeCast Email Security
MimeCast Email Security is a cloud-based solution, which enables businesses in education, manufacturing, legal, healthcare, financial services, construction and other industries to enforce information security policies, block mali...Read more about MimeCast Email Security
Proofpoint Email Protection
Proofpoint Email Protection
Proofpoint Email Protection is a cloud-based email fraud protection platform. It helps users by detecting, blocking and giving responses to email threats. It also eliminates email fraud using real-time insights. Proofpoint Em...Read more about Proofpoint Email Protection
Security Gateway by MDaemon
Security Gateway by MDaemon
Security Gateway by MDaemon is an anti-spam software designed to help businesses in the healthcare, finance, education, government, transportation and manufacturing sectors detect threats and protect email servers against spam, ph...Read more about Security Gateway by MDaemon
SpamTitan
SpamTitan
SpamTitan is a spam filtering solution that caters to businesses, managed service providers (MSPs) and schools to help them to block spam, viruses, malware, ransomware, phishing attempts and other email threats. The solution can e...Read more about SpamTitan
Paubox Email Suite
Paubox Email Suite
Paubox is a cloud-based, HIPAA-compliant email solution provider that helps small to midsize health care businesses send and receive emails. It provides several modules, including Email DLP suite, which protects data and assures c...Read more about Paubox Email Suite
Barracuda Email Security Gateway
Barracuda Email Security Gateway
Barracuda Email Security Gateway is an email security solution, which enables businesses in healthcare, retail and other sectors to protect critical data from email-borne threats and data leaks. Its outbound filtering and quaranti...Read more about Barracuda Email Security Gateway
Area 1
Area 1
Area 1 Horizon is a secure email gateway software designed to help businesses detect and mitigate phishing attacks across web pages, emails and networks. It provides business email compromise (BEC) filtering functionality, enablin...Read more about Area 1
Sentry Email Defense Service
Sentry Email Defense Service
Sentry Email Defense Service (EDS) is a cloud-based platform designed to help enterprises secure emails against virus, phishing links, spam, DDoS and various other email-borne threats. The solution comes with a multi-layered fil...Read more about Sentry Email Defense Service
Sophos Email
Sophos Email
Sophos Email is a cloud-based solution that helps organizations establish secure email networks and provide protection against intrusion, unauthorized access, malware, and other threats. The platform allows businesses to define cu...Read more about Sophos Email
Mail Assure
Mail Assure
N-able Mail Assure is a cloud-based email security solution designed to help businesses secure incoming and outgoing emails. The protection and filtering engine uses machine learning to protect against various online threats such ...Read more about Mail Assure
ContentCatcher
ContentCatcher
ContentCatcher is a cloud-based, anti-spam and email security solution designed to help businesses of all sizes manage and prevent cyber threats. The centralized platform allows businesses to scan email attachments or URLs for mal...Read more about ContentCatcher
ALTOSPAM
ALTOSPAM
ALTOSPAM is a SaaS email security software that addresses all types of structures (company, public service, association) of all sizes. The principle of operation consists in making transit the flow of messaging of our customers to...Read more about ALTOSPAM
Mailock
Mailock
Exchange confidential information with customers using your existing email setup. Encrypt messages and attachments, and authenticate your recipients. Features include: AES-256 email encryption, multi-factor recipient authenticati...Read more about Mailock
Sealit
Sealit
Sealit solutions provide end-to-end encryption giving full data management to its users with email and file protection. Seamlessly implemented with communication & collaboration tools that you already use. Best for small businesse...Read more about Sealit
Leads And CRM
Leads And CRM
Get new leads fitting all your criteria with the freshly launched solution: Leads and CRM, where it helps you find new leads. This lead generation software is insanely valuable for companies that are looking to tap into a much bi...Read more about Leads And CRM
Abnormal Security
Abnormal Security
Abnormal stops text-only based socially engineered attacks with natural language processing understanding what normal looks like to block never-before-seen attacks. Abnormal has complete visibility into all email traffic, includ...Read more about Abnormal Security
Secure Exchanges
Secure Exchanges
Secure Exchanges allows organizations to exchange, retrieve or sign confidential documents without compromising sensitive information. From Outlook, Office 365, Gmail, CRM, ERP, in-house system, and with Secure Exchanges SDKs, thi...Read more about Secure Exchanges
SpamHero
SpamHero
SpamHero offers a cloud-hosted spam filtering solution that can prevent spam and phishing attacks from reaching your domain. With thousands of filters added daily, SpamHero can detect new spam attacks as soon as they appear on the...Read more about SpamHero
Fortra's Agari DMARC Protection
Fortra's Agari DMARC Protection
Agari Brand Protection allows organizations to ensure security from email spoofing, phishing, and other online threats. A cloud-based solution, Agari provides DMARC email authentication, enterprise-grade SPF and DKIM that help pr...Read more about Fortra's Agari DMARC Protection
Agari Phishing Defense
Agari Phishing Defense
Agari Phishing Defense is a cloud-based software that helps protect businesses from online attacks — whether that be social engineering, spearphishing and other forms of identity theft. The solution combines behavioral analysis wi...Read more about Agari Phishing Defense
Popular Comparisons
Buyers Guide
Last Updated: March 16, 2023Email is a trusted communication method for organizations worldwide. With the rise of the work-from-home model, emails have now become more crucial for business communication. However, email channels can be hijacked by cybercriminals to infiltrate your business network; steal or corrupt data; and launch phishing attacks, ransomware attacks, and more.
Secure email gateway software can help your business prevent cyberattacks launched via emails. It stops email messages that contain spam, malware, phishing, or fraudulent contents from reaching their intended recipients. It also scans outgoing emails for spam or malware to ensure your business accounts or domains aren’t added to spam blacklists.
Secure email gateways do much more than just protect your email accounts from impersonation or account takeovers. This buyers guide has all the information you need to purchase an email gateway solution that caters to your business requirements.
Here’s what we'll cover:
What is secure email gateway software?
Secure email gateway software is an email security solution that monitors and protects your company’s email servers. It scans the contents of all outgoing and incoming emails to detect and block malicious contents, such as spam, malware, and phishing agents. It helps prevent email data breaches and also lets you meet regulatory compliance and data security standards.
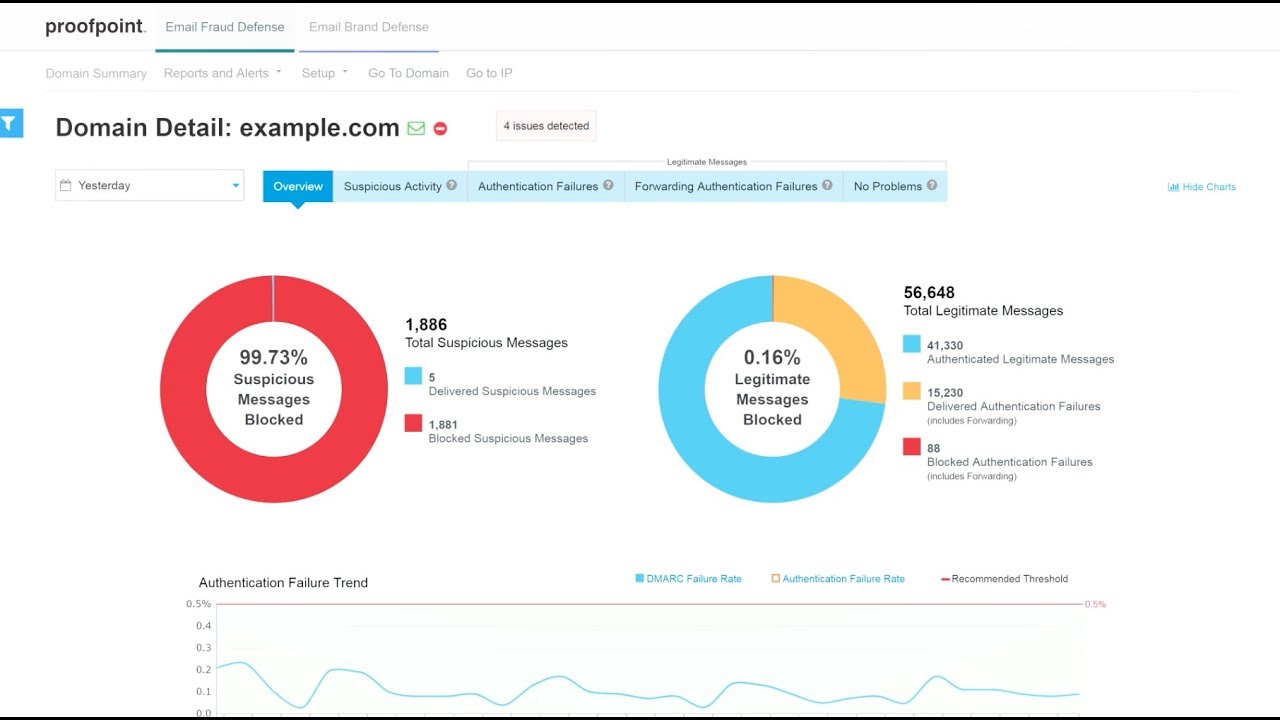
Reporting and analytics in Proofpoint Email Protection (Source)
Common features of secure email gateway software
Software features vary by product or vendor, but most secure email gateway platforms have the following features in common:
Threat protection | Protect email contents, communication, and servers against unauthorized access, malware, phishing attacks, and other threats. |
Email filtering | Filter the contents of inbound emails to identify unwanted, malicious, or unsolicited data and move them to the spam folder. |
Email monitoring | Monitor incoming and outgoing communication to protect against external threats and to ensure sensitive information doesn’t leave your organization. |
Data loss prevention | Protect business-critical data from being lost, misused, or accessed by unauthorized users. The software also helps prevent data breaches and comply with industry regulations. |
Encrypt, or disguise, the contents of sensitive email messages to prevent them from being accessed by anyone other than the intended recipients. | |
Reporting/analytics | Use reporting and analytics to get insights into metrics such as the number of threats detected by the software and the top spam senders. |
Email archiving | Archive email messages for records management, internal audits, regulatory compliance, or future reference. Store the messages in a format that can be digitally indexed, searched, and retrieved. |
Third-party integration | Integrate the secure email gateway software with other tools such as cybersecurity, web security, and cloud security platforms. |
Email continuity | Continue to send and receive emails during unplanned server outages. The software acts as a backup system that can temporarily take the place of your email servers during outages. |
What type of buyer are you?
Before purchasing software, you should assess which buyer category you belong to. The majority of secure email gateway buyers belong to one of the following categories:
Small and midsize enterprises (up to 500 employees): Most small and midsize businesses (SMBs) have a strict security budget. Also, they don’t have a dedicated cybersecurity team to back up critical data or continuously monitor their email servers. Buyers in this category should select a budget-friendly secure email gateway that offers comprehensive protection against malware, spam, phishing, and other common threats. They can even opt for free software versions or trials before making an actual investment.
Large enterprises (over 500 employees): Large businesses have the budget to invest in advanced security solutions. They usually have an in-house security team and dedicated experts to maintain their security networks. They also have more employees than SMBs, making them more prone to human errors that can cause cyberattacks. A fully featured secure email gateway solution that provides encryption and customization would be a good fit for such buyers. These capabilities will allow them to set up customized data leak prevention and filtering policies to monitor the threat landscape continuously for better protection.
Benefits of secure email gateway software
Below is a comprehensive list of benefits you can expect from deploying a secure email gateway solution:
Better protection for sensitive data: Hackers can infiltrate your company’s email channels to target unsuspecting employees and gain access to confidential data. A secure email gateway protects your employees from threats such as viruses, spam emails, and phishing attacks. It not only blocks malicious emails from entering your servers but also encrypts any sensitive data leaving your business networks.
Improved compliance: Email gateway software helps your business meet the various security requirements imposed by regulatory agencies. Features such as email archiving and encryption allow you to back up and save email messages and encrypt outgoing communication that contains sensitive information. These features help ensure compliance with internal email security or data loss prevention policies as well as industry regulations such as the General Data Protection Regulation (GDPR).
Key considerations
Here are a few considerations to keep in mind when selecting an email gateway platform:
Threat intelligence: Email security solutions with threat intelligence capabilities offer advanced real-time threat protection. They not only identify and block malware but also help administrators understand how their networks are being attacked, which mediums are being used, who’s attacking them, and which users are being targeted the most. A secure web gateway with threat intelligence functionality can learn threat patterns in real time to help your business mitigate risks.
Deployment options: Analyze your organization’s needs to check which deployment option will suit you the best—cloud-based, on-premise, or hybrid. Cloud-based software has low upfront costs, requires zero maintenance, and will allow you to scale easily, but your data will be stored in third-party servers. With on-premise software, your IT infrastructure and data will be available onsite, but these tools are expensive and need a dedicated inhouse maintenance team. You can also choose a hybrid model that combines the benefits of both cloud-based and on-premise email security tools. When making a selection, take the maintenance cost, deployment cost, and scalability of all three models into consideration.
Market trends to understand
Here’s a recent trend in the email gateway software market that you should be aware of:
Increasing use of artificial intelligence (AI) and machine learning (ML) for email threat detection. AI- and ML-based email security tools can extract and analyze thousands of email data points to identify common threat patterns in malicious messages. Based on this analysis, they can set rules and blacklist emails they find suspicious. These tools can also get additional insights from observing and analyzing emails in a wider context, i.e., across your company’s email servers, business networks, and cloud environment. This self-learning capability of AI and ML helps detect known threats as well as unknown, evolving threat agents.
Note: The application selected in this article is an example to show a feature in context and is not intended as an endorsement or a recommendation. It has been obtained from sources believed to be reliable at the time of publication.







