Find the best Container Security Software
Compare Products
Showing 1 - 20 of 51 products
Sort by
Reviews: Sorts listings by the number of user reviews we have published, greatest to least.
Sponsored: Sorts listings by software vendors running active bidding campaigns, from the highest to lowest bid. Vendors who have paid for placement have a ‘Visit Website’ button, whereas unpaid vendors have a ‘Learn More’ button.
Avg Rating: Sorts listings by overall star rating based on user reviews, highest to lowest.
A to Z: Sorts listings by product name from A to Z.
OX Security
OX Security
Designed for businesses in banking, information technology, financial services and other industries, OX Security is a cloud security platform that provides advanced threat detection and response capabilities. The solution provides...Read more about OX Security
CloudPassage Halo
CloudPassage Halo
CloudPassage Halo is a security solution that helps brands and businesses in finance, e-commerce, healthcare, gaming, B2B SaaS, biotech and digital media sectors safeguard cloud infrastructures. The CloudPassage Halo allows users ...Read more about CloudPassage Halo
Anchore
Anchore
Anchore is a container security solution that helps DevOps teams scan and analyze software containers for vulnerabilities and ensure security through action plans, policy-based compliance and API-based automation. Administrators...Read more about Anchore
ThreatWatch
ThreatWatch
ThreatWatch is a cloud-based solution that helps businesses conduct risk assessments and identify potential vulnerabilities across applications. Professionals can utilize natural language processing (NLP) algorithms to collect dat...Read more about ThreatWatch
Google Container Security
Google Container Security
Google Container Security is a cloud-based solution that helps businesses secure container environments across Anthos, Google Kubernetes Engine (GKE) and Google Cloud Platform (GCP). Professionals can isolate workloads in a sub-VM...Read more about Google Container Security
Falcon
Falcon
CrowdStrike is a cloud-based endpoint protection solution, which assists small to large businesses with anti-virus protection and device control. Key features include AI-based testing, data security and threat event detection. ...Read more about Falcon
CloudGuard
CloudGuard
CloudGuard is a container security solution that helps businesses handle posture management, vulnerability assessment and workload protection operations. It enables DevOps teams to identify compliance risks and security threats, d...Read more about CloudGuard
Tenable.io
Tenable.io
Tenable.io is a cloud security solution that helps businesses in the energy, transportation, automotive, education, retail, finance and other industries streamline operations related to vulnerability management, incident response,...Read more about Tenable.io
OpenShift
OpenShift
OpenShift by Red Hat is a Kubernetes container platform designed to help businesses manage application development and deployment processes. IT operators can gain insights into the cluster's health, inventory, capacity and other m...Read more about OpenShift
WhiteSource
WhiteSource
WhiteSource is the leading solution for agile open source security and license compliance management. It integrates with your development environments and DevOps pipeline to detect open source libraries with security or comp...Read more about WhiteSource
Lacework
Lacework
Lacework is a cloud-based platform that provides intrusion detection, compliance and automated threat defense for multi-cloud containers and workloads. The platform includes password requirements, multi-factor authentication and u...Read more about Lacework
Threat Stack
Threat Stack
Threat Stack is a cloud-based security platform designed to helps enterprises detect and respond to risks across system infrastructure and applications in real-time. Features include audit log, single sign-on (SSO), user managemen...Read more about Threat Stack
Dynatrace
Dynatrace
Dynatrace is an AIOps solution designed to help businesses automate multi-cloud processes and streamline collaboration across multiple teams through purpose-built use cases. Its filtering capabilities enable supervisors to search ...Read more about Dynatrace
Qualys Cloud Platform
Qualys Cloud Platform
Qualys Cloud is a network security management software designed to help businesses monitor IT assets and prioritize threats in real-time. Administrators can receive alerts regarding vulnerabilities, suspicious activities and attac...Read more about Qualys Cloud Platform
Sysdig
Sysdig
Sysdig is driving the standard for cloud and container security. The company pioneered cloud-native runtime threat detection and response by creating Falco and Sysdig as open source standards and key building blocks of the Sysdig ...Read more about Sysdig
Snyk
Snyk
Snyk is an application security and testing platform designed to help businesses find, prioritize and remediate vulnerabilities across open source libraries, codes and containers. The platform enables developers to scan and test...Read more about Snyk
StackRox
StackRox
StackRox is a Kubernetes and container security platform, which helps businesses and government agencies protect cloud applications and manage processes related to network segmentation, incident response and more. The platform let...Read more about StackRox
Orca Security
Orca Security
Designed for organizations operating in the cloud who need complete, centralized visibility of their entire cloud estate and want more time and resources dedicated to remediating the actual risks that matter, Orca Security is an a...Read more about Orca Security
Heroku
Heroku
Heroku is a cloud-based application development platform that supports multiple programming languages. It helps developers effectively manage and scale applications written in open language frameworks and sources. The application ...Read more about Heroku
Argon
Argon
Argon’s first-to-market holistic security solution protects the integrity of software development environments’ CI/CD pipelines, eliminating risks from misconfigurations, vulnerabilities, and preventing major scale software supply...Read more about Argon
Popular Comparisons
Buyers Guide
Last Updated: March 16, 2023Containers are standard software packages used to build, test, and deploy applications on multiple environments. They include all the required executables, binary codes, libraries, and configuration files except the operating system image. This makes them lightweight and portable. Also, they offer agile deployment capabilities and need less coordination and oversight than on-premise or virtualization infrastructure.
Despite these benefits, containers create security challenges. You have to secure the container host, the applications within the container, and the container management stack, among others. To address these security issues, you can use a container security software platform.
Container security software scans containers for vulnerabilities and policy violations and provides remediation for any identified threats. It’s used to secure the various components of containerized applications, such as container images and code repositories, along with their infrastructure and connected networks.
In this buyers guide, we explain what container security software is, its common features and benefits, and the considerations and trends you should keep in mind during software selection.
Here's what we'll cover:
What is container security software?
Container security software is a software tool that helps businesses manage and secure containerized files, applications, systems, and their supporting networks. It protects the cloud computing infrastructure running containerized applications from vulnerabilities in the IT environment. It simulates attacks from common threat actors to detect container vulnerabilities more thoroughly rather than simply relying on standard security scans.
The software provides centralized information about the entire container environment, including details of the docker engine and client, plugins, image registries, and image metadata. It also has an access control mechanism that allows administrators to decide which users can access the containerized data and apps.
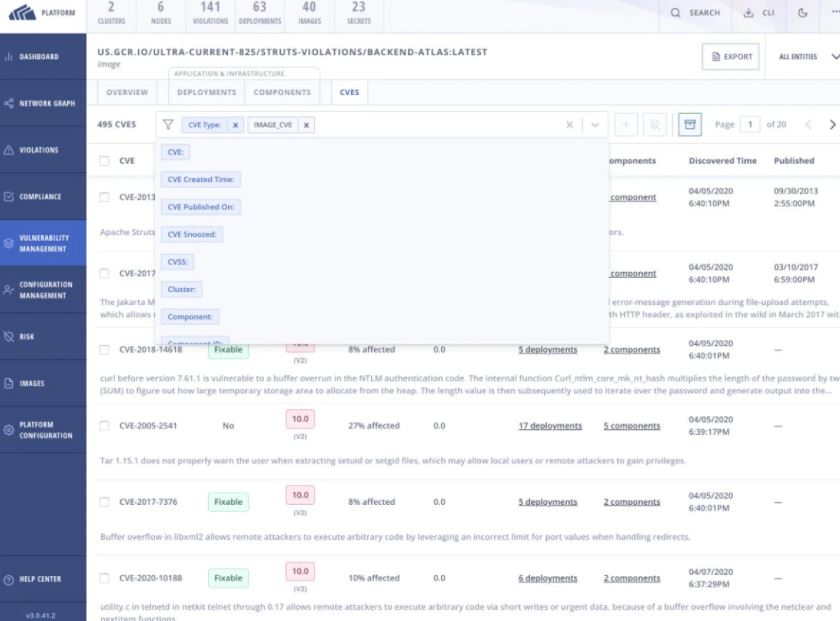
Security vulnerability management in StackRox (Source)
Common features of container security software
Here are some common features of container security software:
Container scanning | Scan container images or pods deployed to production for vulnerabilities or compliance issues. |
Vulnerability management | Detect, classify, prioritize, and mitigate threats and vulnerabilities to your containerized applications. |
Policy management | Enforce security policies to block the use of container images that are vulnerable to threats or incidents. |
Continuous integration (CI) | Integrate the software with container registries and orchestration platforms. CI establishes a consistent and automated way to build, package, and test applications. |
Container inventory visibility | Gather topographic information about container projects—images, image registries, deployments, runtime behavior, and containers spun from the images—to get complete visibility into your container inventory. |
Runtime security | Ensure security during the runtime phase of deployment. This added layer of security helps detect and respond to security threats to the containers running in your environment. |
Compliance | Address security challenges in containers to ensure they’re compliant with standards such as the Center for Internet Security (CIS) and Service Organization Control 2 (SOC 2) benchmarks. |
Security alerts | Receive real-time security alerts when new issues are reported or when vulnerable components are added to your container stacks. |
Priority scoring | Assess security risk across your IT environment and assign priority scores to them to focus your remediation efforts. |
What type of buyer are you?
Understanding the different types of buyers will help you identify your needs better and make an informed purchase. The majority of buyers in the container security market belong to one of the following categories:
Small and midsize enterprises (up to 500 employees): Small and midsize businesses (SMBs) have fewer users and IT assets compared to large enterprises and a strict security budget to follow. They need a tool that can regularly scan their container infrastructure for common and potential threats and vulnerabilities. They should opt for an open source container security system with auditing functionality to detect vulnerabilities early on in the app development process. Cloud-native tools that don't require substantial investment for infrastructure maintenance would be a good choice for these buyers. Container scanning, policy-based admission control, and vulnerability management are a few recommended features for this category.
Large enterprises (over 500 employees): Large enterprises have more users and IT assets than SMBs. Therefore, their container security needs are more extensive. These buyers also have the resources and budget to invest in advanced IT security. They should opt for a full-featured container security suite to ensure protection across the container lifecycle. Automatic vulnerability detection; containerized application security from build time to runtime; integration with container security options; support for different container formats; and active threat prevention across servers, containers, and other microservices are some advanced features they should look for.
Benefits of container security software
Listed below are the key benefits of using container security software:
Better visibility into potential threats: Cybercriminals are coming up with new ways to break into business networks, and container security software helps you stay up to date with these new developments. It offers the ability to detect and prevent security breaches even during runtime and protects your organization against the evolving threat landscape. It also sends real-time security alerts when new issues are reported or when vulnerable components are added to your container stacks.
Secure application development: The tool’s image scanning feature ensures that the containers you use as building blocks during application development are reliable and secure against common threats. It scans the container contents to look for issues ahead of development and also performs checks before the containers are deployed to production. It’s an automated process that helps identify issues as you develop your application and its containers.
Remediation based on threat urgency: Container security software assesses risks across the IT environment and assigns a priority score to each risk. It offers an in-depth analysis of the vulnerabilities in your network, the potential threats they can cause, their level of urgency, and how they can be resolved. Based on this analysis, you can prioritize your remediation efforts to first attend to the most critical vulnerabilities.
Key considerations
Let’s go through a few considerations you should keep in mind when selecting a container security tool:
Functionality: Assess your security needs and decide if you need a tool for container scanning, for serverless function scanning, or for both. For serverless security, the software you select should work well with the serverless computing services that you’re already using, such as AWS Lambda or Azure Functions. And for container security, you’ll have to ensure the software runs smoothly with container deployment tools such as Docker and Kubernetes.
Integration options: The container security solution you choose should integrate well with your existing enterprise security software and practices, such as security information and event management (SIEM) and identity management tools, DevOps practices, and container registries. An integrated tool will provide a feedback loop to shift left (i.e., scan and analyze container images early in the DevOps process), offering continuous guidance to your development and operations teams.
Infrastructure protection: Containers help implement workload-level security, but they also introduce new infrastructure components and unfamiliar attack surfaces. Therefore, ensure you select a container security solution that secures the cluster infrastructure and orchestrator as well as the containerized applications they run. Also, check if the tool is compliant with regulations such as the National Institute of Standards and Technology (NIST) 800-53 and Payment Card Industry Data Security Standard (PCI DSS).
Market trends to understand
Here’s a recent trend in the container security software market that you should be aware of:
Container scanning is emerging as a security best practice for DevOps. Developers are looking for ways to deliver a faster continuous integration and continuous delivery (CICD) pipeline. Container scanning is becoming a part of this “shift left” strategy that supports scanning and analyzing container images early on in the DevOps process to identify vulnerabilities. This reduces the number of tools used and streamlines operations and controls that are built in from the start. Organizations can use these security tools during the pre-deployment phase to address potential security risks and make it safely into production. Because of these benefits, the container scanning approach is emerging as a security best practice for DevOps.
Note: The application selected in this guide is an example to show a feature in context and is not intended as an endorsement or a recommendation. It has been taken from sources believed to be reliable at the time of publication.







