Best Threat Intelligence Software of 2026
Updated March 19, 2026 at 9:47 PM
- Popular Comparisons
- Buyers Guide
Compare Products
Showing 1 - 25 of 161 products
Compare Products
Sort by
Reviews: Sorts listings by the number of user reviews we have published, greatest to least.
Average Rating: Sorts listings by overall star rating based on user reviews, highest to lowest.
Alphabetically (A-Z): Sorts listings by product name from A to Z.


All-in-One Platform to Detect, Understand, and Respond to Risk AlertMedia is purpose-built to enable fast, confident decision...Read more about AlertMedia
AlertMedia's Best Rated Features
See All
AlertMedia's Worst Rated Features
See All


The Heimdal Threat-Hunting and Action Center is threat intelligence solution that is designed to manage and respond to cyber thr...Read more about Heimdal Threat-hunting & Action Center
No reviews yet


Netwrix StealthINTERCEPT helps businesses promptly uncover and prevent attempts to compromise AD security such as unauthorized L...Read more about Netwrix Threat Prevention
No reviews yet


At Versa, our focus is to help simplify how you protect users, devices, sites and connect them to workloads & applications, anyw...Read more about Versa SASE


Log360 is a SIEM or security analytics solution that helps you combat threats on premises, in the cloud, or in a hybrid environm...Read more about ManageEngine Log360
ManageEngine Log360's Best Rated Features
See All
ManageEngine Log360's Worst Rated Features
See All

GoodAccess is a cybersecurity platform (SASE/SSE) that empowers medium-sized enterprises to easily implement Zero Trust Architec...Read more about GoodAccess
GoodAccess's Best Rated Features
See All
GoodAccess's Worst Rated Features
See All

Keepnet's Extended Human Risk Management (xHRM) platform is a comprehensive cybersecurity solution designed to address the human...Read more about Keepnet Labs
Keepnet Labs's Best Rated Features
See All
Keepnet Labs's Worst Rated Features
See All

Malwarebytes for Business is a cloud-based cybersecurity suite comprising Malwarebytes Endpoint Protection and Malwarebytes Endp...Read more about Malwarebytes for Business
Malwarebytes for Business's Best Rated Features
See All
Malwarebytes for Business's Worst Rated Features
See All

#1 Global Leader in Data Resilience We keep businesses worldwide up and running. From secure backups to intelligent data insi...Read more about Veeam Data Platform
Veeam Data Platform's Best Rated Features
See All
Veeam Data Platform's Worst Rated Features
See All

Designed with Fortune 500 and Global 2000 companies in mind, SentinelOne is a leading autonomous cybersecurity platform speciali...Read more about SentinelOne
SentinelOne's Best Rated Features
See All
SentinelOne's Worst Rated Features
See All

Designed for organizations operating in the cloud who need complete, centralized visibility of their entire cloud estate and wan...Read more about Orca Security
Orca Security's Best Rated Features
See All
Orca Security's Worst Rated Features
See All

Avanan is an email security platform designed to help businesses track and monitor applications including Microsoft Office 365, ...Read more about Avanan

ESET Endpoint Security software offers robust cybersecurity solutions for organizations with 250+ employees. This versatile appl...Read more about ESET Endpoint Security
ESET Endpoint Security's Best Rated Features
See All
ESET Endpoint Security's Worst Rated Features
See All

DNSFilter is a cloud-based cybersecurity software that helps businesses leverage AI technology and DNS protection to streamline ...Read more about DNSFilter
DNSFilter's Best Rated Features
See All
DNSFilter's Worst Rated Features
See All

Keeper is a cloud-based business security solution that offers multi-tenant password management and secure file storage. It offe...Read more about Keeper Security
Keeper Security's Best Rated Features
See All
Keeper Security's Worst Rated Features
See All

Automox is the Autonomous Endpoint Management platform built for autonomous from day one. Policy-driven, human-controlled autom...Read more about Automox
Automox's Best Rated Features
See All
Automox's Worst Rated Features
See All

Perimeter 81 is the first Cybersecurity Experience Platform to streamline SASE through its groundbreaking ease-of-use and unifie...Read more about Perimeter 81
Perimeter 81's Best Rated Features
See All
Perimeter 81's Worst Rated Features
See All

Teramind offers employee monitoring, insider threat detection, and data loss prevention (DLP) solutions. Teramind UAM monitors u...Read more about Teramind
Teramind's Best Rated Features
See All
Teramind's Worst Rated Features
See All

Blackpoint Cyber is a technology-focused cybersecurity company headquartered in Maryland, USA. The company was established by fo...Read more about Blackpoint MDR
Blackpoint MDR's Best Rated Features
See All
Blackpoint MDR's Worst Rated Features
See All

NordVPN is a computer security software designed to help businesses encrypt internet connectivity to securely access personal in...Read more about NordVPN
NordVPN's Best Rated Features
See All
NordVPN's Worst Rated Features
See All

INLYSE Malware.AI is a visual AI-based malware detection solution that uses cutting-edge technology to detect malware. It offers...Read more about INLYSE Malware.AI
INLYSE Malware.AI's Best Rated Features
See All
INLYSE Malware.AI's Worst Rated Features
See All

IPQS is a leading fraud prevention solution tailored for businesses like yours. Powered by the most up-to-date and comprehensive...Read more about IPQS

EcoTrust introduces an innovative CAASM platform that redefines cybersecurity by focusing on prioritizing critical business risk...Read more about EcoTrust
EcoTrust's Best Rated Features
See All
EcoTrust's Worst Rated Features
See All

Powered by Zero Trust Architecture, Appgate secure access and cybersecurity solutions enable businesses to reduce risk and ensur...Read more about Appgate SDP

Protegent Antivirus is a security platform that provides protection for computer systems. It safeguards against a range of malwa...Read more about Protegent Antivirus
Popular Comparisons
Buyers Guide
This detailed guide will help you find and buy the right threat intelligence software for you and your business.
Last Updated on January 27, 2025Within the first 10 months of 2019, 140 local governments, police stations, and hospitals suffered ransomware attacks. Among the prominent attacks in 2019 were the stealing of data of about 100,000 people from a federal subcontractor for U.S. Customs and Border Protection, and the compromise of hundreds of thousands of Asus computer owners via a secret backdoor planted in the computer maker's Live Update tool.
As an IT administrator or business owner/manager you can no longer rest assured that you've bought the costliest firewall or antivirus to protect your digital fronts. It’s no longer enough to react quickly—being proactive about threats and staying up-to-date with the latest in cybersecurity is the need of the hour. That's where threat intelligence software comes in.
This buyers guide will explain to you the basics of such tools.
Here’s what we’ll cover:
What is threat intelligence software?
Threat intelligence software is a tool that gives organizations a near real-time view of the threat landscape by identifying existing and evolving threat vectors. It helps you keep your security standards up to date and improve your network performance with detailed information on threats to specific networks, infrastructure, and endpoint devices. The tool can help you mitigate the risk of breach in security or loss of data, thus helping you build an effective defense mechanism and reducing the risk of damage to your reputation and bottom line.
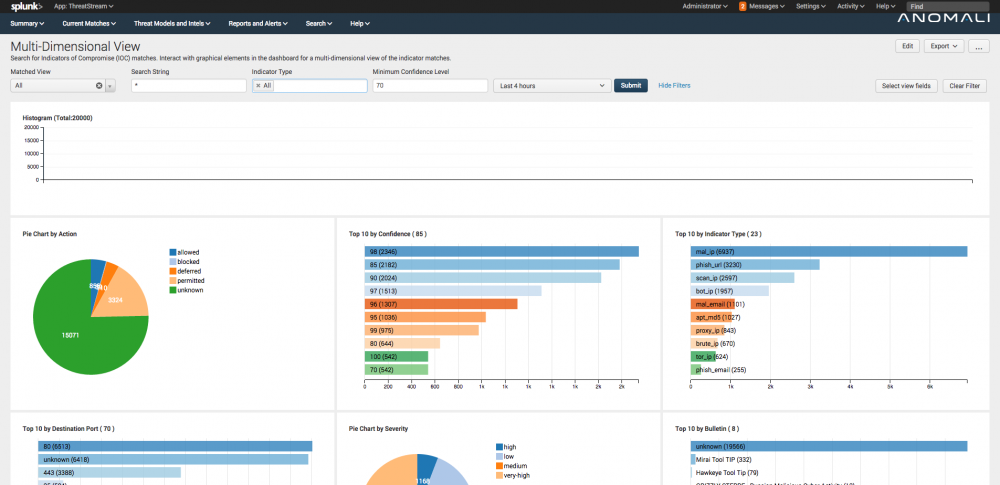
Dashboard in Anomali (Source)
Common features of threat intelligence software
Continuous monitoring | Monitor multiple resources within the network in real-time or near real-time, and use data for threat detection. |
Threat detection | Identify threats based on current and historical data from various resources within the network. Some tools also apply machine learning to ensure appropriate detection and reduce false positives. |
Threat alerts | Receive alerts whenever there is a potential threat to the network, with details on the source of the threat. |
Automatic threat remediation | Set an automatic response mechanism for when there is a potential threat. |
Response prioritization | Prioritize response to threats based on different security levels. |
Reporting | Generate detailed and customized reports on the security performance of your network and information such as threat frequency, severity, and intelligence status. |
Issue tracking | Manage and maintain a list of issues (or potential threats) over a period of time—also known as incident tracking. |
What type of buyer are you?
The capabilities of threat intelligence solutions can vary depending on their intended industry and use-case. While some solutions such as IBM X-Force Exchange, LogRhythm, and FireEye can be applied to a diverse range of industries and use-cases, others such as LookingGlass and Anamoli are more appropriate for industry-specific use-cases.
Hence, before you select a solution, it's important to understand what type of buyer you are.
Organizations that operate within a niche industry: The threat intelligence of specific industries like finance, insurance, healthcare, media, or energy in typically very specific and usually have definite compliance requirements laid out by governments and industry bodies.
If your organization falls in this category, you should explore solutions that are designed with industry-specific threats and compliance in focus.
Organizations that are not industry-specific: Such organizations could either be operating in more than one industry, or might not be dealing with sensitive customer data. They also likely don't have industry-specific compliance requirements.
If your organization falls in this category, a generic threat intelligence solution with basic features such as monitoring, threat detection, and remediation would suffice your needs.
Benefits of threat intelligence software
Threat intelligence software helps you identify potential threats to your network and protect against security breaches and cyber attacks ahead of time. Its benefits are as follows:
Minimize risk of security breach: Gain insight into immediate and evolving cyber threats faced by your organization and take measures to prevent security breaches. Also, safeguard against potential loss of data.
Stay up-to-speed with potential threats: Cybercriminals continue to come up with new ways of hacking and breaking into secure networks everyday. Threat intelligence software helps you stay up-to-date with these developments and protect your organization against evolving threats.
Prioritize response based on urgency of threat: Get a thorough understanding of the vulnerabilities in your network, the potential threats they cause, their level of urgency, and how they can be resolved. Then, respond to the vulnerabilities accordingly.
Key considerations when purchasing threat intelligence software
The right threat intelligence software can not only ensure the security of all your data and network, but also save you a lot of money. However, picking software for your organization can get tricky. Here are a couple of points to keep in mind:
Don't over- or under-purchase: It is easy to get confused between threat intelligence software, security information and event management (SIEM) solutions, and vulnerability management solutions. While SIEM and vulnerability management solutions can provide some information similar to threat intelligence products, they also include features such as event correlation and incident response. Pick a software that is apt for your needs and not one that provides too many or too few features.
Weigh deployment options thoroughly: The deployment and delivery of the solutions can vary widely, from cloud-based (private, public, or hybrid clouds) to on-premise. Evaluate the deployment of the solutions and their cost implications thoroughly before choosing one.
Note: The applications selected in this article are examples to show a feature in context and are not intended as endorsements or recommendations. They have been obtained from sources believed to be reliable at the time of publication.