Best Identity Management software of 2026
- Popular Comparisons
- FrontRunners
- Buyers Guide
Compare Products
Showing 1 - 25 of 236 products
Compare Products
Sort by
Reviews: Sorts listings by the number of user reviews we have published, greatest to least.
Average Rating: Sorts listings by overall star rating based on user reviews, highest to lowest.
Alphabetically (A-Z): Sorts listings by product name from A to Z.

ManageEngine ADAudit Plus is a Windows auditing, security, and compliance solution. Key features include comprehensive logon aud...Read more about ManageEngine ADAudit Plus
ManageEngine ADAudit Plus's Best Rated Features
See All
ManageEngine ADAudit Plus's Worst Rated Features
See All

Deel is the only global-first people platform that enables companies to hire, relocate, pay, manage, equip, and support talent i...Read more about Deel
Deel's Best Rated Features
See All
Deel's Worst Rated Features
See All

Rippling is an integrated workforce management platform that unifies HR, IT, and finance tools to streamline operations. It cent...Read more about Rippling
Rippling's Best Rated Features
See All
Rippling's Worst Rated Features
See All

GoodAccess is a cybersecurity platform (SASE/SSE) that empowers medium-sized enterprises to easily implement Zero Trust Architec...Read more about GoodAccess
GoodAccess's Best Rated Features
See All
GoodAccess's Worst Rated Features
See All

Shared computer access control with 2FA and automatic user-switching. Login to shared computers using phoneless-2FA and automati...Read more about GateKeeper Enterprise

Conecta Suite is the ideal solution for those looking to maximize the potential of Google Workspace and boost team productivity....Read more about Conecta Suite
Conecta Suite's Best Rated Features
See All
Conecta Suite's Worst Rated Features
See All

Zluri is a data-driven enterprise SaaS management platform that facilitates discovery, management, optimization, and compliance ...Read more about Zluri
Zluri's Best Rated Features
See All
Zluri's Worst Rated Features
See All

Trusona is a leader of passwordless MFA solutions for enterprises within the financial services, healthcare, higher education, m...Read more about Trusona

Avatier Identity Anywhere is a cloud-based identity management solution designed to help businesses manage their employees' digi...Read more about Avatier Identity Anywhere

Zygon is an all-in-one platform that automates the management of applications and accounts for modern IT and security teams. It ...Read more about Zygon
Zygon's Best Rated Features
See All
Zygon's Worst Rated Features
See All

TDS Visitor is an industry-leading enterprise visitor management solution that provides a unified view of all visitors across mu...Read more about Acre Security

Twilio User Authentication & Identity offers digital identity verification and intelligence tools to build mutual trust between ...Read more about Twilio User Authentication & Identity
Twilio User Authentication & Identity's Best Rated Features
See All
Twilio User Authentication & Identity's Worst Rated Features
See All

LogMeOnce is a cloud-based password and identity management solution that enables businesses of all sizes to manage login creden...Read more about LogMeOnce
LogMeOnce's Best Rated Features
See All
LogMeOnce's Worst Rated Features
See All

Foxpass is a cloud-based and on-premise platform that helps small to large enterprises automate threat detection and access cont...Read more about Foxpass

Powered by Zero Trust Architecture, Appgate secure access and cybersecurity solutions enable businesses to reduce risk and ensur...Read more about Appgate SDP

Under.io is a powerful software solution that simplifies customer onboarding and signing digital agreements. Our platform suppor...Read more about Under

Persona offers a best-in-class unified identity platform that gives organizations the building blocks they need to design and ma...Read more about Persona
Persona's Best Rated Features
See All
Persona's Worst Rated Features
See All

Integrity Advocate is an identity verification, participation monitoring, and exam proctoring solution. This solution protects l...Read more about Integrity Advocate

Corma is the access management solution crafted to simplify your software ecosystem and streamline your IT operations. With Corm...Read more about Corma

AppViewX AVX ONE CLM is a comprehensive, automated certificate lifecycle management (CLM) solution that simplifies PKI and certi...Read more about AppViewX AVX ONE CLM

heylogin is the password solution for your business. A smartphone swipe instead of a master password makes your everyday life pa...Read more about heylogin

Trust Swiftly is a cloud-based identity verification platform that helps businesses verify their customers with over 15 identity...Read more about Trust Swiftly

AWS Identity and Access Management (IAM) is a policy and identity management solution that helps businesses streamline processes...Read more about AWS Identity and Access Management (IAM)

Workforce Identity Verification Built for the IT Service Desk FastPass Identity Verification Manager (IVM) FastPass Identity Ver...Read more about FastPass IVM
FastPass IVM's Best Rated Features
See All
FastPass IVM's Worst Rated Features
See All

ReACT is a cloud-based solution that helps organizations establish automated processes to reset, identify, authenticate and sync...Read more about ReACT
ReACT's Best Rated Features
See All
ReACT's Worst Rated Features
See All
Popular Comparisons
Your Guide to Top Identity Management Software, August 2023
Software Advice uses reviews from real software users to highlight the top-rated Identity Management products in North America.
Learn how products are chosenExplore FrontRunners
“Usability” includes user ratings for Functionality and Ease of Use.
“Customer Satisfaction” includes user ratings for Customer Support, Likelihood to Recommend and Value for Money.
Reviews analysis period: The reviews analysis period spans two years and ends the 15th of the month prior to publication.
Buyers Guide
This detailed guide will help you find and buy the right identity management software for you and your business.
Last Updated on January 27, 2025You probably take a number of steps to protect your identity on a day-to-day basis. Your bank accounts, utilities accounts and even your social media accounts are all password-protected to make sure nobody but you can access them. You're wise to do this, because in today's world to have your identity stolen online means suffering a great deal of havoc that might take you months, if not years, to correct.
So why should you be any less careful when it comes to identity protection at your small-to-midsize business (SMB)? It can be just as dangerous and disastrous in your business life as in your personal life if an unauthorized person should gain access to your SMB's private information.
That's where identity management software comes in.
Identity management software manages who within your company can access information, keeping out unauthorized users as well as specifying levels of access for different individuals.
This guide will explain what you need to know about this software, and what you need to consider when choosing the right identity management system for your SMB.
Here's what we'll cover:
What is Identity Management Software?
Common Features of Identity Management Software
What is Identity Management Software?
Identity management software plays a massive role in the overall cyber-security of your SMB. It can be used to provide access to vital information, documents and other content for specific employees, while keeping others restricted to a lower level of access. In addition, it ensures that everyone granted any access is actually whomever they say they are.
More generally, identity management is the process of controlling information about users on computers, including the information that authenticates user identity and grants/limits authorization to each individual user.
Identity management software is particularly important in a business environment where so much important data and information can be accessed by a large variety of stakeholders independently.
In order to make sure that the people who need that information are able to get to it when they need to do so, while at the same time preventing outside forces from finding or accessing that information, identity management is a requirement of any modern business operation, including SMBs like yours.
Other terms that you may see used interchangeably for “identity management systems" include:
Access governance systems
Identity and access management systems
Entitlement management systems
User provisioning systems
Common Features of Identity Management Software
Below is a table listing some of the most common features of identity management software. Most of these features relate to how access is granted and/or restricted to certain users, and different vendors and systems may utilize different methods to this end:
Access Control | Creates a gated wall that must be surpassed in order to access certain information. As a result, access can be authorized or restricted for certain persons across different locations and systems, allowing the right people to gain access to information and keeping the wrong people from getting their hands on that information. This is the core functionality of identity management software. |
Single sign-on (SSO) | Allows users to log into a system just one time (rather than multiple times over the course of a session) using a single ID and password. The user may move between different connected systems once they have signed on, but they don't need to enter a new ID/password (or re-enter the same one) in order to do so. |
Multi-factor authorization | Asks for multiple, independent data components from a user before they can gain access to the system. Typically this requires a user to both enter their password as well as an encrypted, randomly generated code, created on demand when they enter that password and sent to them via text message or email. |
Password management | Assists users in generating complex passwords (either by storing them in an encrypted database or creating them on demand) and retrieving lost or forgotten passwords. This function will also typically provide self-help to users who are having trouble signing in. |
Directory Services | Creates a central point from which access can be managed by administrators, granting certain users specific levels of access to data (and restricting all others from accessing that same data). |
Multi-factor authorization will frequently require users to provide an independent form of verification, such as a separate email address or a phone number. That text message authentication may look something like this:
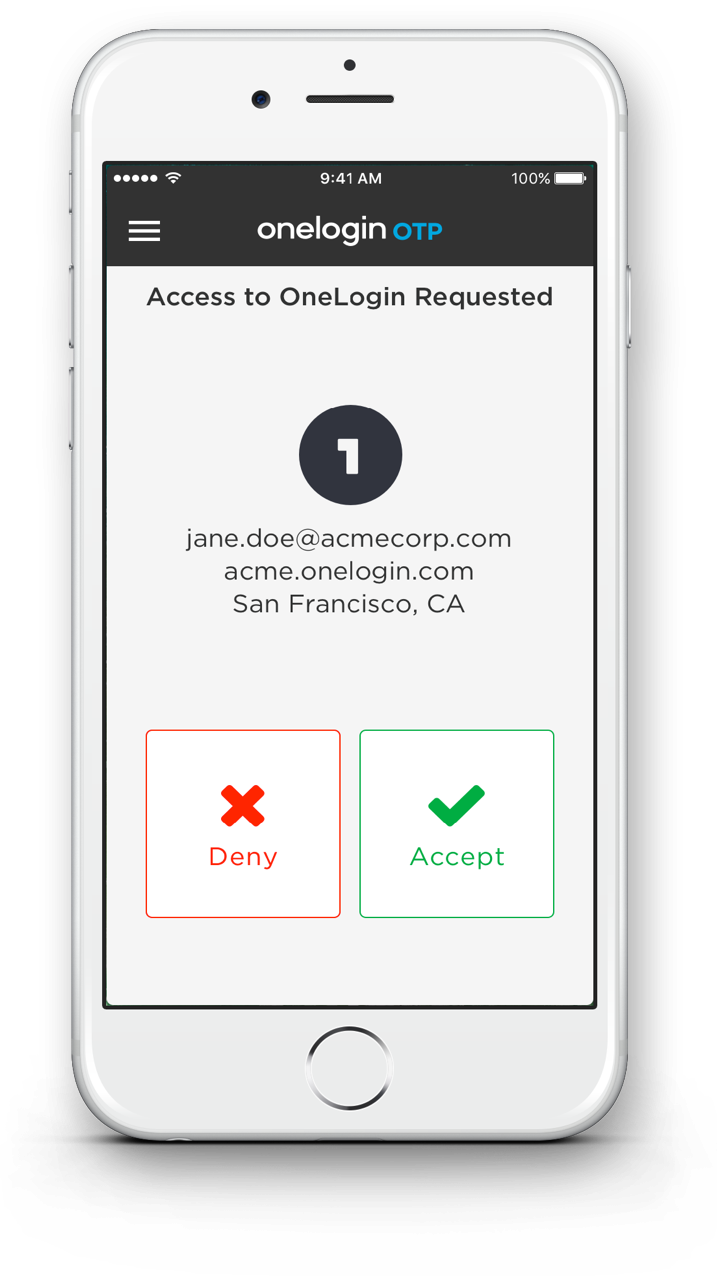
Onelogin's multi-factor “adaptive authentication", sent via text message.
Key Considerations
Other factors to take into consideration when picking the best identity management software for your business include:
Will my users require varying levels of access? At larger, enterprise-level companies, a key component of identity management software is the functionality that grants/restricts access to certain information for certain individuals. Your much smaller SMB may not have the same need to restrict information. If you only have a handful of employees who all have equal access to your data, for example, you may be able to purchase a simpler, cheaper identity management system that doesn't allow you to create restrictions.
Do I want a single sign-on system? If you're more concerned with security than you are with ease of use for your employees, then you may not want to use an SSO system, thus requiring users to enter IDs and passwords at multiple times during their journey through the system. This can be a major annoyance, however; for this reason, most identity management software vendors provide SSO as their main offering.
Do I want a multi-factor system? If you want to make sure your system is secure, you should look for a multi-factor system that will require users to have both their password and access to a backup form of identification (like a separate email address or a phone number to which an access code can be sent).
Does this system integrate with my other software? Creating a gateway to your company's database/intranet/internal systems is only useful if that gateway can actually connect to the software that you're already utilizing. Many of these systems have their own forms of identity management already built in, so you'll want to have an in-depth discussion with your vendor about how their identity management product will fully integrate with all your other software systems.

